Pwnagotchi is an A2C-based “AI” powered by bettercap that learns from its surrounding WiFi environment in order to maximize the crackable WPA key material it captures (either through passive sniffing or by performing deauthentication and association attacks). This material is collected on disk as PCAP files containing any form of crackable handshake supported by hashcat, including full and half WPA handshakes as well as PMKIDs.
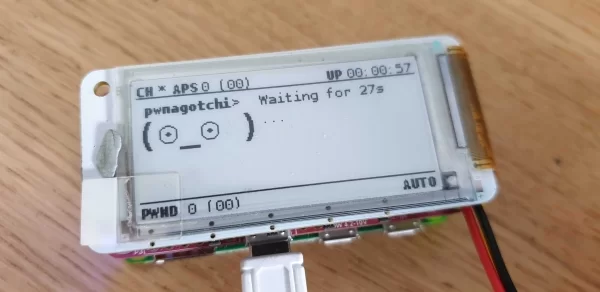
Combined with the PaPiRus pHAT display, it makes the perfect little companion for sniffing local Wi-Fi network. Moreover, why not make it portable? We also added the PiJuice pHAT to the Pi Zero, with an additional LiPo battery allowing us to take this little gadget anywhere on the move.
Note: This tool is to be used for wireless penetration testing and must not be used for anything malicious
What you need
Getting Started
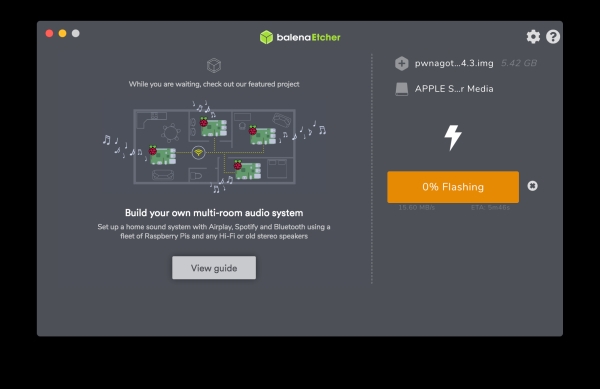
Step 1 – Header over to https://github.com/evilsocket/pwnagotchi/releases and download the latest pre-compiled image. Once downloaded Flash to your microSD card using Balena Etcher.
Step 2 – Before inserting the SD card into the Raspberry Pi we need to create a configuration file that the software will load on boot. You may need to eject the SD card and insert it into your computer again. Create a new file in the boot partition of the SD card called “config.yml” and add the following:
main:
name: 'pwnagotchi'
whitelist:
- 'YourHomeNetworkMaybe'
plugins:
grid:
enabled: true
report: true
exclude:
- 'YourHomeNetworkMaybe'
ui:
display:
enabled: true
type: 'papirus'
color: 'black'
Change “YourHomeNetworkMaybe” to your Wi-Fi SSID if you wish to exclude your Wi-Fi from the search.
Step 3 – Before we insert the SD card we need to assemble the hardware. Connect a stacking header to the Pi Zero:
Source: Build a Pwnagotchi WiFi penetration tester with Pi Zero and a PaPiRus display

