The goal of this project is to learn as much as possible about the Zsun WiFi card reader and run OpenWrt on it to turn it into an awesome wifi device.
UPDATE 2016-04-23 The new PCB is missing a jumper on the RX serial line, see serial port section
UPDATE 2016-03-16 The second PCB revision has identical software and hardware (apart from optimized minor component layout), flashing works the same
UPDATE 2016-03-12 We now know that there are at least two different PCB versions of the reader!
UPDATE 2016-02-21 github mirror at https://github.com/Emeryth/openwrt-zsun
UPDATE 2016-01-27 informatic seems to have figured out how to use the original firmware's update function: Zsun Card Reader Firmware Update Format
People Involved
-
emeryth (emeryth at hackerspace.pl) ← contact me about the project
-
q3k (q3k at hackerspace.pl)
-
informatic (informatic at hackerspace.pl)
Current status
All the important aspects of hardware are understood.
OpenWrt Chaos Calmer ported (but not yet thoroughly tested), can be flashed over telnet if you dare.
What can I do with it?
-
Use it for its intended purpose of serving files, duh
-
Use as a tiny and pretty good WiFi AP/client/repeater (the hardware supports multiple simultaneous wireless interfaces!)
-
Play around with OpenWrt
-
Use it as the brains of your IoT project
-
Buy a dozen and play around with mesh networking
-
Use it for distributed WiFi activism like PirateBox or OccupyWiFi, or run a minimal Tor hidden service (with addition of being easily hidden in public places)
-
Host Node.js on it and take your apps to your favorite coffee shop :^)
Size comparison with a single 18650 cell powerbank.
Hardware
-
AR9331 SoC
-
64MB RAM
-
16MB SPI Flash
-
GL827L USB SD Card Reader
The device consists of two PCBs sandwiched together and connected via 8 pins.
The bottom PCB contains only the SD card reader chip and SD slot, it can be safely removed without affecting operation.
Serial Port
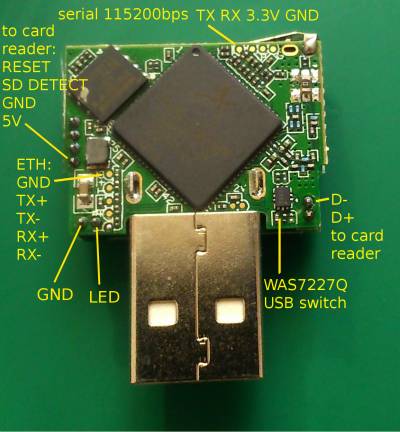
The serial console is brought out on testpoints (see pictures). Bitrate is 115200.
Original firmware root password is “zsun1188”
The new PCB has a missing jumper that connects the serial RX testpad to the SoC. Short it or solder directly to the lower pad of the jumper to use serial. (The second missing resistor is a pull up/down, I guess)
Thanks to Andreas H. for the clear picture of the new PCB.
Ethernet Port
There are testpoints for connecting an ethernet port (eth1 of the SoC).
Use a Magjack or similar connector with magnetics.
This port is required for uploading images to u-boot.
USB switch
The device contains a WAS7227Q USB switch, which connects the sd card reader chip to either the USB plug, or the AR9331 SoC.
The switch is controlled with GPIO21. Set pin to LOW to connect card reader to SoC.
GPIO
-
GPIO0 – LED
-
GPIO18 – card reader reset
-
GPIO21 – USB switch
-
GPIO22 – card detect
Hardware hacking
If you remove the card reader board you get easy access to one USB port and 3 GPIO pins. Remember that GPIO is 2.5V!
GPIO pins and bootstrap
Here's a closeup of the bootstrap GPIO pins, perhaps useful if you want to try enabling USB device mode.
Bootstrap functions:
-
GPIO 0 : Crystal frequency of external clock 0=25, 1=40 MHz
-
GPIO 1 : Booting from internal 0=ROM, 1=SPI Flash
-
GPIO 11: 0=General JTAG, 1=CPU ICE
-
GPIO 12/28 : external memory type (00=SDR, 01=DDR, 10=DDR2)
-
GPIO 13: USB mode 0=device, 1=host
-
GPIO 16: Download firmware from 0=USB, 1=MDIO
USB device mode
AR9331 is capable of working as a usb device (gadget). Unfortunately the code for that exists only as a patch for an old version of OpenWrt: http://neykov.name/posts/ar933x-usb-device-driver/
So if you want to use the zsun as a USB gadget you will need to:
-
Port the code
-
Remove the bootstrap resistor setting USB to host mode
-
Remove the card reader PCB and rewire the the USB signal pins
Original firmware
The original firmware is full of holes, including an always on telnet backdoor on port 11880. Source: http://www.zoobab.com/zsun-sd11x-wifi-card-reader
Regular telnet might not work (netkit-telnet in Ubuntu 15.10 works fine) but you can connect using socat:
$ socat - TCP4:10.168.168.1:11880
������!����
(none) login: root
root
Password: zsun1188
Welcome to
------- | / /--/ ___ |
/ | /| \/ _____ --|--|
/_____\ |--- --|-- //--/ / / |
__|__ | /|\ / \/ /___\ / |
___|___ ___|____ / | \ / / \|
深圳至上移动科技有限公司
Shenzhen Zsun Cloud Technology Co., LTD.
www.zsuncloud.com
BusyBox v1.01 (2014.12.27-02:50+0000) Built-in shell (ash)
Enter 'help' for a list of built-in commands.
~ #
If you want to use proper telnet just run it on different port with:
telnetd -p 2137
OpenWrt
WARNING Still under development
My OpenWrt port, based on the 15.05 “Chaos Calmer” release:
https://code.hackerspace.pl/emeryth/openwrt_zsun/
You have to clone the “zsun” branch
git clone -b zsun https://code.hackerspace.pl/emeryth/openwrt_zsun/
Github mirror: https://github.com/Emeryth/openwrt-zsun
Compiled images and image builder:
https://owncloud.hackerspace.pl/index.php/s/7s5c5RDS7Njgwpv
You cannot use kernel modules from the official repository, use the image builder or compile them yourself if they're not included.
This port sticks to the original flash layout.
I've added a few things to this port to make it more usable on the zsun without having to solder.
-
Wifi is enabled by default, AP mode, no encryption
-
Entering failsafe will run a script that automatically does a factory reset
-
The SD card detect pin is registered as a button and will trigger failsafe when inserted/removed during boot
-
The SD card reader is reset every time a card is inserted or removed
Backing up the original firmware
At the end of the flash chip there is an “ART” partition that contains calibration data for wifi, you want to have a backup of this.
You can backup the entire flash over telnet by using dd.
dd if=/dev/mtd0 of=/tmp/mtd0.bin
Do this with all the mtd partitions (mtd0 to mtd5)
Then make a symlink to /tmp in /etc/disk so you can download the files via the web interface.
ln -s /tmp /etc/disk
Flashing
Here are some ways you can flash the device:
-
Solder on an ethernet jack and flash from the original uboot (hard but safe)
-
Reflash the bootloader from the original firmware to one that supports upload over serial (less soldering but fatal if you mess up)
-
Reflash the firmware from the original firmware using mtd_write (easy but you have to do it right on the first try)
-
Attach a programmer to the flash chip (impossible to mess up)
-
Use the original firmware's update function
Flashing with original uboot
Attach an ethernet jack and serial cable, setup a TFTP server on your PC with a static IP 10.168.168.10
Then at the uboot prompt enter the following commands:
For More Details: Hacking the Zsun WiFi SD Card Reader