In the modern business environment, many employees are traveling or working from home. To compensate for this, many companies offer a VPN service, where employees can access a company's private network over the internet. This offers a secure method of accessing this information through an encrypted tunnel. The VPN service also allows remote management of networking devices, functionality of applications off-site, and the ability to work remotely without sacrificing the integrity of the network. In a smaller business, the budget for this project will be a lower figure, which may present a problem.
Project Description:
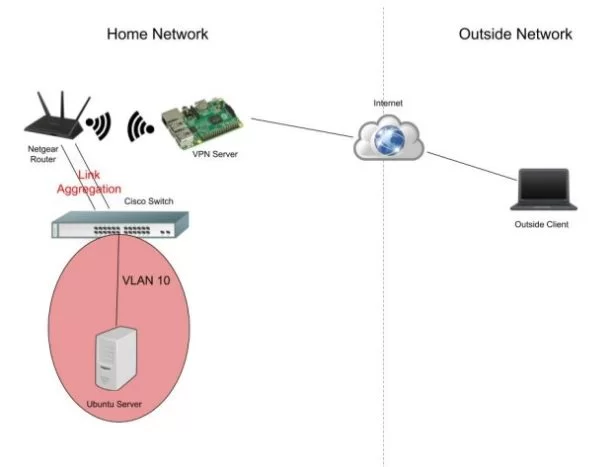
In order to present a simple, cheaper solution to the problem above, a network will be designed for remote access. With the use of open-source firmware, providing the main functions of the network is still possible, without spending a fortune. This project will consist of a network with a router, a Cisco switch, an old laptop running a Ubuntu server, and a Raspberry Pi running an OpenVPN server. This solution is for a smaller business with a basic network setup already in place. By adding a Raspberry Pi and making it the VPN server, it solves the issue of remote access, without adding more stress on the router. Running a VPN server from the router of the network would be the first solution, but it also eats away at the CPU. In this lab, a simple network will be set up with a router connected to an ISP, with the ability to act as an access point for wireless devices. The Netgear router will be connected to a Cisco switch with two aggregated links for trunking. A PC, with a Ubuntu machine running Samba will be connected through a wired Ethernet connection. The server will be placed into a separate VLAN to segment the traffic. A Raspberry Pi running OpenVPN will be connected wirelessly to the router, using the 2.4 GHz signal. The basic functions of the router have already been configured before the semester started. This includes, DHCP, wireless capabilities, and DNS functions. After the VPN and NAS servers have been configured, port forwarding will be configured to the servers and a separate gateway will be added for the new VLAN. A trunk link will also be placed between the switch and router and configured with link aggregation.
Location of Work:
- Home
- Remote Network
Necessary Equipment:
- Raspberry Pi 3 Model B
a. Raspbian Lite
b. Used to run an OpenVPN server - Netgear R6400 Router
a. DD-WRT firmware
b. Used to route traffic towards the VPN and Linux servers - Cisco 2960G Series Switch
a. Used to create VLAN database - Ubuntu Server (NAS)
a. Stores files on the network
b. Used to test connectivity throughout the network
- Laptop
a. Windows 10 operating system
b. Used to test connectivity off-site, through the VPN
c. Tracks interfaces with Wireshark
d. Creates a backup on the NAS remotely
Network Diagram:
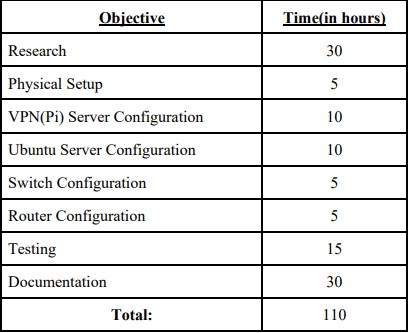
Specific Objectives:
- Research
a. Raspbian operating system
b. PiVPN (OpenVPN) configuration
c. Ubuntu NAS configuration
d. DD-WRT port forwarding
e. Windows backup to network server
- Physical Setup
a. Connect the router to the modem, leading to the ISP
b. Connect Raspberry Pi to the router wirelessly
c. Connect the NAS to the switch - VPN Server Configuration
a. Install Raspbian operating system
b. Configure PiVPN
c. Assign a static IP address
d. Use a dynamic DNS service to assign a DNS to the Pi (do to ISPs changing your
public IP address frequently)
e. Select UDP protocol for faster speeds - Ubuntu Server Configuration
a. Install Ubuntu OS on the system
b. Assign a static IP address (in VLAN 10 subnet)
c. Install Samba
d. Configure the NAS
i. Folders (Admin, Finance, Sales)
ii. Files (Backups in “Admin”)
e. Configure appropriate account permissions
i. Admin account (can view and edit all)
ii. Finance account (can view and edit only “Finance” folder)
iii. Sales account (can view and edit only “Sales” folder)
- Switch Configuration (Removed due to error)
a. SSH configuration
b. Port security configuration
c. VLAN 10 configuration
d. Trunk/access ports
e. STP and Portfast configuration - Router Configuration
a. Install DD-WRT operating system (pre-installed)
b. Link aggregation to switch
c. VLAN gateway
d. Static IP for VPN server
e. Static IP for Ubuntu server
f. Configure port forwarding for VPN and Ubuntu servers - Testing
a. Copy over VPN files onto a USB drive
b. Download OpenVPN on windows laptop
c. Import the connection file
d. Connect remote device to external network
e. Start Wireshark
f. Visit a non-secure web page while tracking the interface
i. In the details, there should be readable text
g. Connect to home network using VPN tunnel
h. Visit a non-secure web page while tracking the interface
i. In the details, there should not be readable text where there was before
i. Access the NAS by IP to browse the folders
j. Make a backup of the Windows PC in the “Backup” folder within the “Admin”
folder with the computer name attached to the file
Applied Knowledge:
The knowledge needed to complete this project combines all of the CCNA/CCNP courses
taken this far, starting with the need for proper port security on the layer 2 switch. More
CCNA/CCNP knowledge used will be to configure the VLAN, SSH, STP, and trunk/access
ports. Security knowledge will also be used in testing the connection to the VPN server to ensure
the tunnel is completely encrypted by using Wireshark. Lastly, Linux knowledge will be used to
set up the Ubuntu server and Samba file sharing, although it will expand beyond the coursework.
A challenge presents itself while using a Raspberry Pi to create a VPN connection into
the network. Another challenge comes with using Cisco best practices on a non-Cisco device, the
Netgear R6400 router. The security practices learned in the Cisco classes at Akron will need
translated into the DD-WRT firmware and applied correctly. The knowledge will also have to
expand beyond the realm of the coursework when configuring and securing the VPN connection,
something not practiced in any classes. Lastly, knowledge of Windows backups to a network
drive will be needed while testing the connection to the internal network.
Analysis:
As the project began, configuration of the switch and router was first up on the list of devices because, this handles the VLAN for the servers, establishes the link aggregation, and connects the devices to the internet using their own subnet. The router configuration went smoothly, and at first, it seemed like the switch configuration would be able to allow them to communicate. However, this is where the error occurred, where the router was trying to communicate with the switch, but no communication could be established. The configurations were reset on both devices, troubleshooting went on for hours and days, but inevitably the Cisco 2960G Switch had to be removed from the project. The issue seems to steam from the older IOS
on the Cisco device, as this is the only logical reasoning and no more time could be dedicated
towards troubleshooting the issue. The project still needed to be finished on time and the only
way to do that was to use the router to provide the access VLANs. The upgraded topology can be
seen in the figure below:
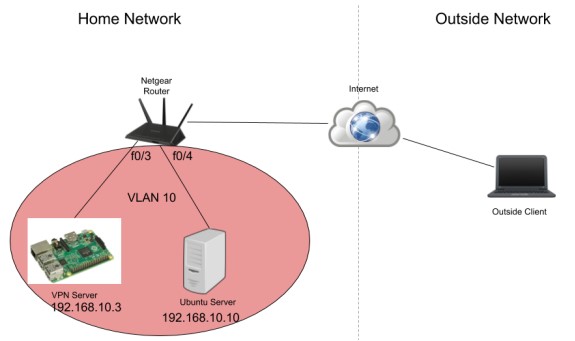
Although the topology needed to change due to the error, all of the new ideas are still intact. In fact, it provided a need for more research in using a Linux router and using it like a layer 3 switch, where it can handle routing abilities and a VLAN database. Configuring the Cisco device has been done in all the CCNA/CCNP courses, so there wasn’t anything new in that topic, so removing the switch was beneficial in more than one way. The main purposes of this project were to experiment with Linux devices, since it was not completely covered in networking courses, and to do this as cheaply as possible for all the small businesses out there who have a tighter budget. The total cost can be found in the figure below:
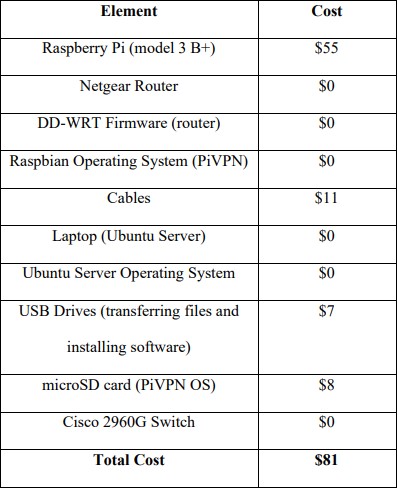
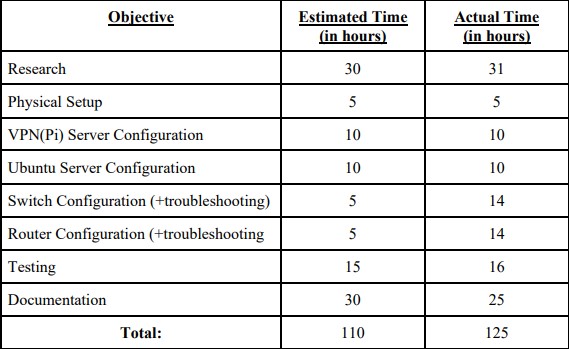
The rest of the project, following the removal of the switch, went smoothly and the network was able to be tested successfully. The whole network worked correctly including the authentication for both servers, encryption over the VPN connection, and port forwarding on the router. This project is proven to be beneficial for a small business looking to use their current infrastructure to allow remote access for all employees. Remote access would be relevant in today’s current society, with the COVID-19 forcing many employees to work from home to protect themselves and their loved ones. Every small to medium sized business could utilize this method as necessary, given the current circumstances. A chart for estimated versus actual time spent on this project can be seen in the figure below:
Source: Budget Remote Access VPN & NAS

