Do you hate it when the internet goes down in your area? Do you want to be notified when your internet goes down when you are away from home? Do you have a project that needs 100% internet availability where you would need to be notified of service disruption?
This guide will show you how use FONA as a secondary cellular connection to the internet with automatic failover and real time notifications.
I built a home security system to set off an alarm and notify me in the event of an intruder break in. The home security system requires an internet connection to route a message to my phone when the house is under attack. In the event of an internet outage someone could break into my house without my knowledge. To resolve this issue, I wrote a service to monitor my primary internet connection. When the service detects an internet outage it will automatically reroute all outbound traffic over a cellular network using the Adafruit FONA. A message will then be sent to my phone over the data plan to let me know my that my data plan is actively being used to route traffic. Once the primary internet connection is available, the data plan will no longer be used and all traffic will be automatically routed back to the primary interface.
Prerequisites
For Raspberry Pi and BeagleBone Black, follow the FONA Tethering Setup Guide to install and configure the Point-to-Point Protocol daemon for Fona.
If you are already familiar with the tethering setup guide and installing ifacefailover on a fresh Raspberry Pi, in the next section you can execute the bin/raspberryPiInstall.sh script instead of the bin/install.sh script to automatically disable the kernel's use of the hardware serial connection, install ppp, and download the Fona ppp peer prior to installing the ifacefailover service.
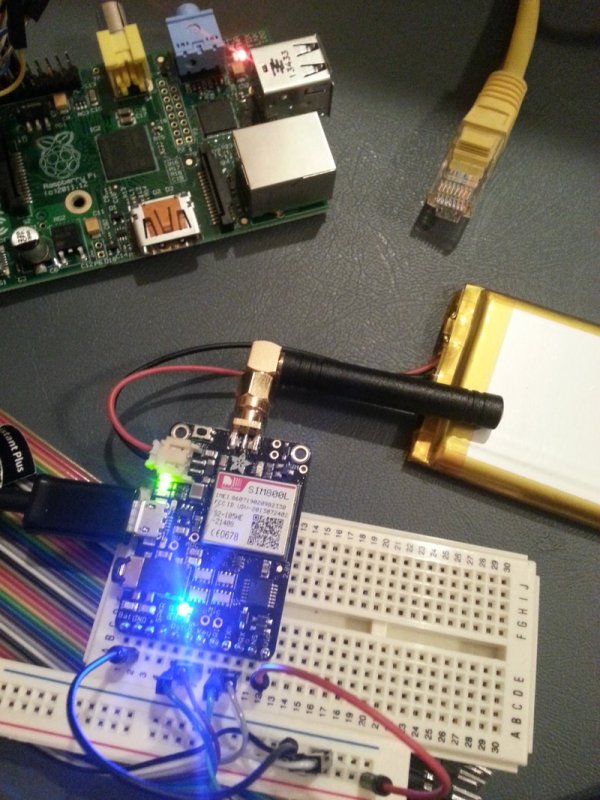
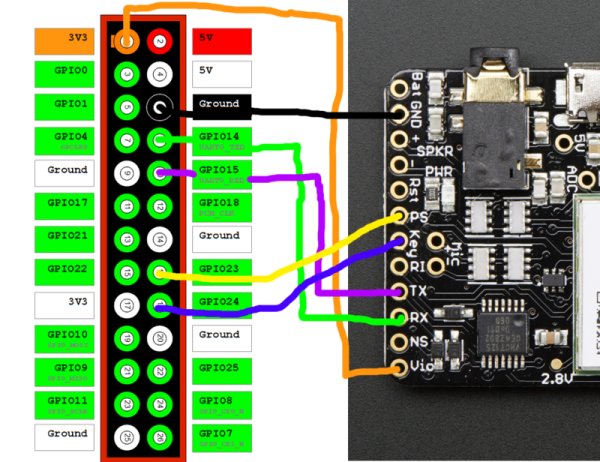
Wiring
Raspberry Pi to Fona
Power Status (PS) and Key pins are tied to GPIO pins so the Fona can be turned on and off programmatically. Your data plan is only used in the event of a failover.
ifacefailover Service
Install the Source Code
We will be using the open source python service ifacefailover to monitor a network interface and reroute all outbound network traffic to Fona in the event of an outage. Clone the ifacefailover repository from GitHub and execute the install.sh script from the bin directory. This will create the appropiate directory structure under /opt, link to the recently checked out source code, install the required python dependencies, and create the startup service /etc/init.d/ifacefailover. The following commands should be executed on the device you wish to install ifacefailover.
- sudo mkdir –p /opt/git/ifacefailover
- sudo git clone https://github.com/shellbit/ifacefailover.git /opt/git/ifacefailover
- sudo /opt/git/ifacefailover/bin/install.sh
Routes
Routes are how your device connects to the internet and other devices. Routes are established on a network interface through an ethernet cable, wireless card, or even UART pins. ifacefailover routes are configured in the ifacefailover.properties file. You can define as many failover routes as you wish. The order you define the routes in the properties file matters! The first route defined in the properties file is your primary route. The ifacefailover service will always try to restore connection to your primary route in the event of a failover. If your primary route goes down, ifacefailover will try to failover to your secondary route. If your primary route and secondary route are down, ifacefailover will try to failover to your tertiary route, and so on and so forth until it detects an available route. You can view the current routes on a Linux device by running the following command. ifacefailover simply rewrites your default route (0.0.0.0) to a different gateway and interface in the event of a failover.$ route –n
- Kernel IP routing table
- Destination Gateway Genmask Flags Metric Ref Use Iface
- 0.0.0.0 192.168.1.1 0.0.0.0 UG 0 0 0 wlan0
- 192.168.1.0 0.0.0.0 255.255.255.0 U 2 0 0 wlan0
Route Verifiers
ifacefailover uses Route Verifiers to determine if a route is healthy and capable routing packets. Route verifiers are implemented as python classes and must return a boolean value to determine if the route is available. We will be using an ICMP route verifier to send ping echo request packets to target servers outside our network. Route verifiers are not limited to ICMP requests. We could have used HTTP, a raw socket connection, or even implemented our own custom protocol to verify the route. Checkout the ifacefailover wiki on GitHub for more examples and if you write a route verifier that could be used by others, please consider contributing it to the ifacefailover open source project.
Route Handlers
Route Handlers provide hooks into the ifacefailover service. They allow you to log failover events, send event notifications, start or stop running processes, and anything else you want to do throughout the lifecycle of the route. You can associate as many route handlers as you wish to a route. We will be using the Log Handler to log events, the HTTP Handler to send failover events to the Google Cloud Messaging service, and the Fona Raspberry Pi Handler to turn the Fona on and off pre and post failover. Checkout the ifacefailover wiki on GitHub for more examples and if you write a route handler that could be used by others, please consider contributing it to the ifacefailover open source project.
Property Configuration
Routes, Route Handlers, and Route Verifiers must be configured in the ifacefailover.properties file. To configure a route, open the /opt/ifacefailover/config/ifacefailover.properties file in your favorite editor. This property file contains key/value pairs of properties used by the ifacefailover service. The route configuration format is route.name.property=value. So the property route.primary.gateway=192.168.1.1 means configure a route named primary and set its gateway property to 192.168.1.1. Below are a list of configurable route properties.
For more detail: Network Infactere Failover using FONA